
Conservative estimates put company’s monthly income at a minimum $500,000.
According to a recently released report, researchers at Checkpoint blame an Italian “company” CloudEyE for the widespread malware, GuLoader. The company has formerly advertised itself as “DarkEye” and “DarkEye Protector.”
To make matters interesting, the company isn’t a totally illicit dark web entity. It exists in plain sight on the internet as a legitimate business operation, and even has VAT registration numbers:
SD SOFTWARE DI DRAGNA SEBASTIANO FABIO – Via Paolo Bentivoglio, 17 – Catania (CT) – Partita IVA: 05276750873. EasySoft Di IVANO MANCINI – Via Lombardia, 8 – Fonte Nuova (RM) – Partita IVA: 13379111001
GuLoader is a heavily used “network dropper” in 2020, used to distribute malware through cloud services like Google Drive, Dropbox, etc.
The following infographic shows GuLoader has been used to distribute different strands of malware like Formbook, Azorult, Remcos, NanoCore, Lokibot, among many others.
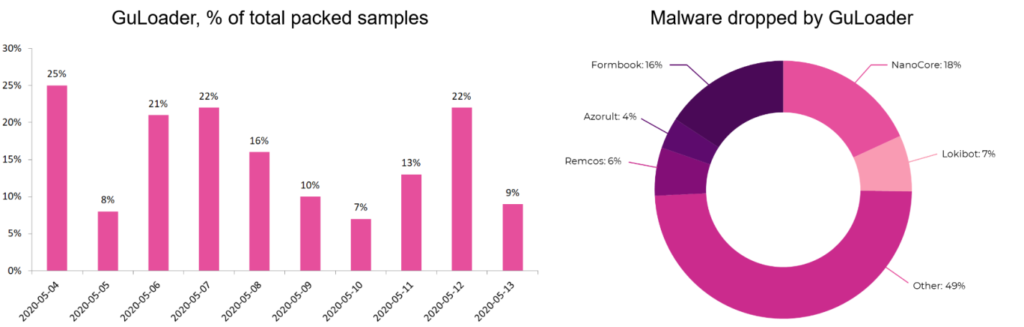
Image credit: Checkpoint
The discovery was made by Checkpoint researchers while reverse engineering what was detected as GuLoader malware samples. There were references to “DarkEye protector” in those binaries.
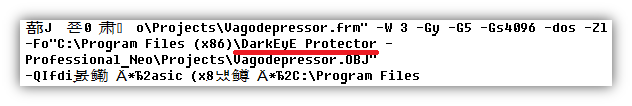
Image credit: Checkpoint
On taking a closer look, it was clear that GuLoader and DarkEye are very similar samples with payload embedded in the sample itself – therefore no download was necessary.
Moreover, when searching the web for “DarkEyE Protector,” different threads on hacker forums made it easy for the researchers to corroborate facts and conclude that DarkEye and CloudEye were purposely created with the intention of evading malware detection, therefore helping attacks. The report reads:
“The ads describe DarkEyE as a crypter that can be used with different malware such as stealers, keyloggers, and RATs (remote access Trojans), and makes them fully undetectable for antiviruses (FUD). This left us with no doubt that this software was developed to protect malware from discovery by anti-viruses, as the authors didn’t forget to emphasize that they “don’t take any responsibility for the use” of DarkEyE.”
The entity behind CloudEye or DarkEye appears to be a legitimate business, as evident from their website www.securitycode.eu. They market themselves with the intention of, “protecting windows applications from cracking, tampering, debugging, disassembling, dumping.”
Moreover, given their “plans” start at $100/month and the entity claims to have upwards of 5,000 customers, their monthly income has been estimated at $500,000, speaking conservatively.
The so-called CloudEye “protector,” however, actually injects malware into your compiled apps. To test, the researchers used a simple “calc.exe.” When “encrypted” using CloudEye, the resulting binary was detected positive for GuLoader.
“The CloudEyE-produced sample that we got has the same structure as GuLoader. Just like GuLoader, it is compiled with Visual Basic and contains shellcode encrypted with a random 4-bytes XOR key. Therefore, we decrypted the shellcode from both samples (CloudEyE and GuLoader),” stated the advisory.
Additionally, CloudEye alters the program structure to make it challenging for automated analysis, detection and decryption to take place:
“To make it harder for automatic analysis and probably also to prevent automatic decryption, the shellcode starts from a random stub and is prepended with a jump over this stub. In both samples, the same space on the stack is reserved for a structure with global variables.”
Checkpoint has been able to trace identities of the people behind the CloudEye operation to specific email addresses, domains and names.
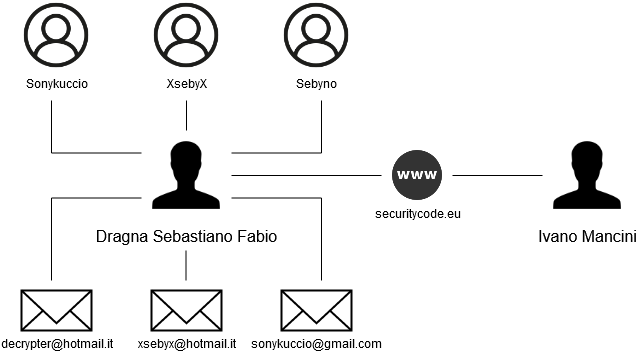
Image credit: Checkpoint
Encryption bypasses virus detection
The report concludes with reasons as to why CloudEye is malicious and why many cloud providers are inconsistent with detecting CloudEye-encrypted binaries:
“CloudEyE operations may look legal, but the service provided by CloudEyE has been a common denominator in thousands of attacks over the past year. Tutorials published on the CloudEyE website show how to store payloads on cloud drives such as Google Drive and OneDrive. Cloud drives usually perform anti-virus checking and technically don’t allow the upload of malware. However, payload encryption implemented in CloudEyE helps to bypass this limitation. Code randomization, evasion techniques, and payload encryption used in CloudEyE protect malware from being detected by many of the existing security products on the market. Surprisingly, such a service is provided by a legally registered Italian company that operates a publically available website which has existed for more than four years.”
A comprehensive list of Indicators of Compromise (IOCs) and malware hashes are available in the same report.
© 2020. Ax Sharma. All Rights Reserved.
Originally published on and syndicated from Security Report.